Should I Turn off NLA?
No!
Network Level Authentication is how Windows authenticates remote desktop clients and servers before sending your credentials over to a remote machine.
If the client can't authenticate the remote server then there's no guarantee it's the server you actually want to log in to, and therefore may be a server trying to steal your credentials.
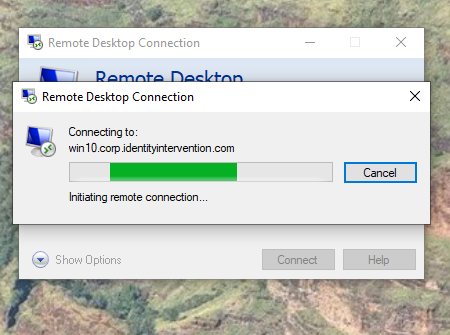
This is why you see a credentials prompt when using RDP and never see the Windows logon screen during the initial connection.
See How Authentication Works when you use Remote Desktop (syfuhs.net) for the gory details.
The whole point of NLA is to make sure the name you typed into the RDP application is in fact the server you've connected to. It fails if it isn't the same server. Without NLA the client has no method to prove the remote server is the same as what you've typed in.
This applies to all forms of credentials, not just passwords. Passwords are ubiquitous so they're the most dangerous to leak, but smart card logons and any number of 3rd party mechanisms can be proxied and snooped if you've turned off NLA. This means an attacker sitting in between your client and server can impersonate users without you ever knowing.
So please think twice about turning off NLA. It's there to protect you.